We carry out penetration tests for companies of different sizes
From small and medium-sized companies to corporations, public administration and critical infrastructure organizations – we carry out tests of all sizes. Up to date, in accordance with standards such as the OWASP Top 10 and based on ISO 27001.






Rely on the expertise of our pentesters, it’s that simple

1. establishing contact & exchanging initial details
Once you have contacted us, we will schedule an initial meeting to discuss your request in more detail. We reserve the desired implementation period subject to reservation and determine the work packages and scope. You will then receive a quote.
2. offer acceptance and kick-off date
Your appointment is reserved as soon as you have accepted the offer. You will receive an order confirmation and all necessary contracts. All necessary information should be available for the kick-off meeting.
3. carrying out the test
We start carrying out the test on the agreed date, which is accompanied by an intensive exchange.
4. dispatch of the report and presentation of the results
We provide you with the report and, if required, we then hold a meeting to present the test results and recommended measures to your technicians and management.

Silas Borgmeier
Account Manager
Distribution
Would you like a personal consultation?
I will be happy to assist you with our expertise.
Our vulnerability scan work packages at a glance
External vulnerability scan
In work package one, the test includes carrying out a vulnerability scan for external systems. Various automated tools are used for this. Among other things, the following weaknesses can be identified:
- Use of outdated software
- Detection of known vulnerabilities
- Use of insecure encryption methods
- Missing HTTP header
- Insecure default credentials
Social engineering methods, such as phishing, are not part of the attack. The aim of this work package is to answer the following questions in relation to the external systems:
- Do systems have known vulnerabilities?
- Can an attacker access confidential data?
- Is an attacker able to change data without authorization?
- Are the systems and their software up to date?
- Can authentication mechanisms be bypassed?
Internal vulnerability scan
In work package one, the test includes carrying out a vulnerability scan on internal systems. Various automated tools are used for this. Among other things, the following weaknesses can be identified:
- Use of outdated software
- Detection of known vulnerabilities
- Use of insecure encryption methods
- Insecure default credentials
- Insecure network and application protocols
- Outdated operating systems
Social engineering methods, such as phishing, are not part of the attack. The aim of this work package is to answer the following questions in relation to the external systems:
- Do systems have known vulnerabilities?
- Can an attacker access confidential data?
- Is an attacker able to change data without authorization?
- Are the systems and their software up to date?
- How secure is the network infrastructure?
An excerpt from our pentesters

Vincent Reckendrees, BSc
Head of Offensive Security
Vincent Reckendrees has been working on the security of web applications for years. Among other things, he holds the OSWP certificate from OffSEc.

Mario Klawuhn, BSc
Senior Offensive Security Consultant
Mario Klawuhn, OSCP, is a highly qualified pentester, who demonstrates his expertise in the detection and elimination of security vulnerabilities.

Tim Barsch, BSc
Offensive Security Consultant
Analyzing internal networks and micro web services is part of Tim Barsch’s day-to-day business. He holds a bachelor’s degree in IT security.
Callback service
Write to us with your request. We will be happy to call you back at a specific time.
Appointment service
Arrange a digital appointment with us so that we can discuss your requirements.
Contact form
Leave a message via our contact form. We will get back to you.
Find out more about our completed projects
Success stories

IT security made in Germany
Attacking and testing applications is the means to an end. The medium-term goal is always to increase the level of IT security and thus enable the long-term protection of customer and company data. We have been awarded the “IT Security made in Germany” seal by the TeleTrust Bundesverband IT-Sicherheit e.V. (German IT Security Association). The document declaring and authorizing the use of the seal is available for inspection.
Even though we operate worldwide, our headquarters will remain in Germany
AWARE7 GmbH has been based in Germany since its foundation. The location in Germany is valued by our international customers due to the high quality standards.
Products and services are free of hidden accesses
All of the services we provide are carried out in accordance with ethical principles. The removal of all access points after a test is mandatory and firmly integrated into the process.
Research & development takes place exclusively in Germany
New products and collaboration with students and scientific institutes are part of our corporate DNA. We are always at the cutting edge of research and development and are based exclusively in Germany.
Plan your next vulnerability scan now
FAQ – Frequently asked questions
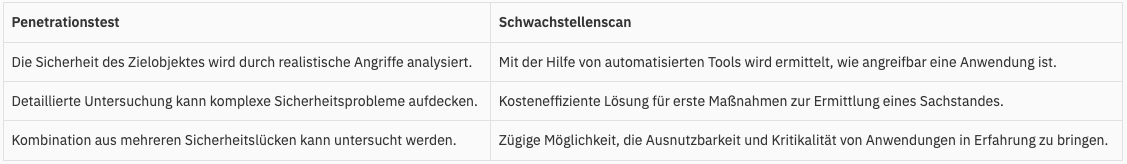
A vulnerability scan is an automated process that examines computer systems, networks and applications for security gaps. The aim is to identify potential vulnerabilities that could be exploited by attackers.
Vulnerability scans are important for detecting and eliminating security gaps at an early stage. They help to minimize the risk of cyberattacks and increase the general security of the IT infrastructure.
It is recommended that vulnerability scans be carried out regularly, at least quarterly or after every significant change to the IT infrastructure. More frequent scans may be necessary if your organization is at high risk.
Vulnerability scans can be applied to a variety of systems and applications, including web applications, networks, servers or databases.
The duration of a vulnerability scan depends on the size and complexity of the environment to be scanned. A typical scan can take from a few hours to several days.
As a rule, vulnerability scans only have a minimal impact on system performance. However, there may be an increased network load during the scan. Scans can often be configured to be performed outside of business hours.
Vulnerability scans can identify a wide range of vulnerabilities, including missing security updates, misconfigured systems, web application vulnerabilities and more.
After a vulnerability scan, you will receive a detailed report listing all identified vulnerabilities. The report also contains recommendations for remedying the security gaps found.
The results of a vulnerability scan are used to prioritize security gaps and take appropriate measures. This can include the installation of security patches, the reconfiguration of systems or other security measures.
Yes, vulnerability scans are secure and are designed not to cause damage to your systems. However, it is important to have the scan carried out by a trustworthy provider.
Yes, vulnerability scans can be carried out internally by your IT team, provided the necessary tools and knowledge are available. Alternatively, you can commission an external service provider such as AWARE7 GmbH.
The cost of a vulnerability scan varies depending on the scope and complexity of the environment to be scanned. Please contact us for a customized offer.
You can book a vulnerability scan using our contact form on the website or contact us directly by phone or email. We will be happy to advise you and create a customized offer for your company.
Before the scan, all relevant systems should be identified and access rights clarified. It is also helpful to have a list of the most important applications and systems to be scanned to hand.