We have already offered live hacking shows for companies of all sizes
The professional preparation and follow-up of events is part of our daily business. We regularly speak to hundreds of people about the business of cyber criminals on the Internet. Don’t take any risks – we put on hundreds of shows a year and can draw on an extensive pool of speakers.





The way to your live hacking show

1. establishing contact & exchanging initial details
After you have contacted us, we will schedule an initial meeting in which we will exchange information. We reserve your event subject to reservation. You will then receive a quote.
2. acceptance of the offer and reservation of the appointment
Your appointment is reserved as soon as you have accepted the offer. You will receive an order confirmation. All event details must now be finalized.
3. individualization, technical check and implementation
Depending on your wishes, we can customize the live hacking show to the target audience, organization or location. If required, we will carry out a technical check and perform the show.
4. editing the recording, sending the slides and invoicing
If the show has been recorded, it will be edited. We can send the films on request. We then take the liberty of invoicing for the service.
Create awareness for the topic of information security
Understanding how hackers think
Digital attacks are diverse. How do criminals think and how can anyone get caught in the digital crosshairs? Find out!
Low-threshold, for every target group
Every live hacking show is only as complex as it needs to be. We guaranteed a target group-oriented approach.
Entertaining with added value
Experience our dynamic show. Live and individual every time. With us you don’t get a PowerPoint battle.
Tips for private and professional life
Give your audience valuable tips and tricks for more digital security in their private and professional lives.
Possible content for your show
A live hacking show has one focus. You can select these focal points. Customized shows are made for you and can cover topics that are not listed.
Attacks on the password
Show your audience how insecure the use of passwords is. Whether guessed or cracked, we show you the challenges of dealing with passwords.
Call ID spoofing
Falsifying telephone numbers on the telephone display is a popular method for criminals to gain authority. We will show you how you can protect yourself.
Phishing attacks & ChatGPT
Sophisticated phishing emails sent to the right person at the right time are a major threat. With the help of AI, we show you live how modern criminals operate on the Internet.
Search engine hacking
Sensitive information can easily be found on the Internet and with the help of search engines. We show you how it works and how you can protect yourself.
WLAN & Network Hacking
Wireless networks can be dangerous for. the confidentiality of information. We show you live which attacks are still possible today.
Ransomware infection
Ransomware is the biggest threat to organizations of all kinds. Suddenly unable to act. Experience with us how lucrative the business is and how quickly infection occurs.
An excerpt from our speakers

Chris
Wojzechowski, MSc
Managing Partner
Chris Wojzechowski is an experienced IT security expert and speaker at AWARE7 GmbH who specializes in cybersecurity training and awareness-raising. With his practical and clear presentation of complex topics, he supports companies and organizations in optimizing their security measures and arming themselves against current threats.

Jan
Hörnemann, MSc, T.I.S.P.
Authorized signatory, Chief Operating Officer
Jan Hörnemann is an authorized signatory and external information security officer (ISB) at AWARE7 GmbH. With his in-depth expertise in IT security and his many years of experience, he helps companies to develop and implement their security strategies to ensure a high level of protection against cyber threats.

Thomas
Henning, BSc, OSCP
Speaker & Penetration Testing Expert
Thomas Henning is a certified OSCP pentester and holds a Bachelor of Science degree. At AWARE7 GmbH, he uses his extensive expertise and analytical skills to uncover security gaps in IT systems and develop customized security solutions.

Benjamin
Krüger, MA
Speaker & expert for digital learning
Benjamin Krüger has many years of experience as a learning expert and holds a Master of Arts (MA). At AWARE7 GmbH, he develops innovative training concepts and programs to sustainably strengthen the awareness and skills of employees in the area of IT security.
Prof. Dr. Matteo Große-Kampmann, MBA
Head of Research & Development
Prof. Dr. Matteo Große-Kampmann is Head of Research and Development at AWARE7 GmbH. With his extensive scientific expertise and innovative approaches, he drives the development of new technologies and security solutions in order to continuously improve IT security and set forward-looking standards.

David
Bothe, MSc
Speaker & IHK Examination Board
David Bothe, MSc, is an experienced IT security expert at AWARE7 GmbH and a member of the IHK examination board. With his in-depth expertise and practice-oriented approach, he makes a significant contribution to education and training in the field of IT security and supports companies in implementing effective security strategies.
Callback service
Write to us with your request. We will be happy to call you back at a specific time.
Appointment service
Arrange a digital appointment with us so that we can discuss your requirements.
Contact form
Leave a message via our contact form. We will get back to you.
Find out more about our completed projects
Success stories
Plan your next live hacking show now
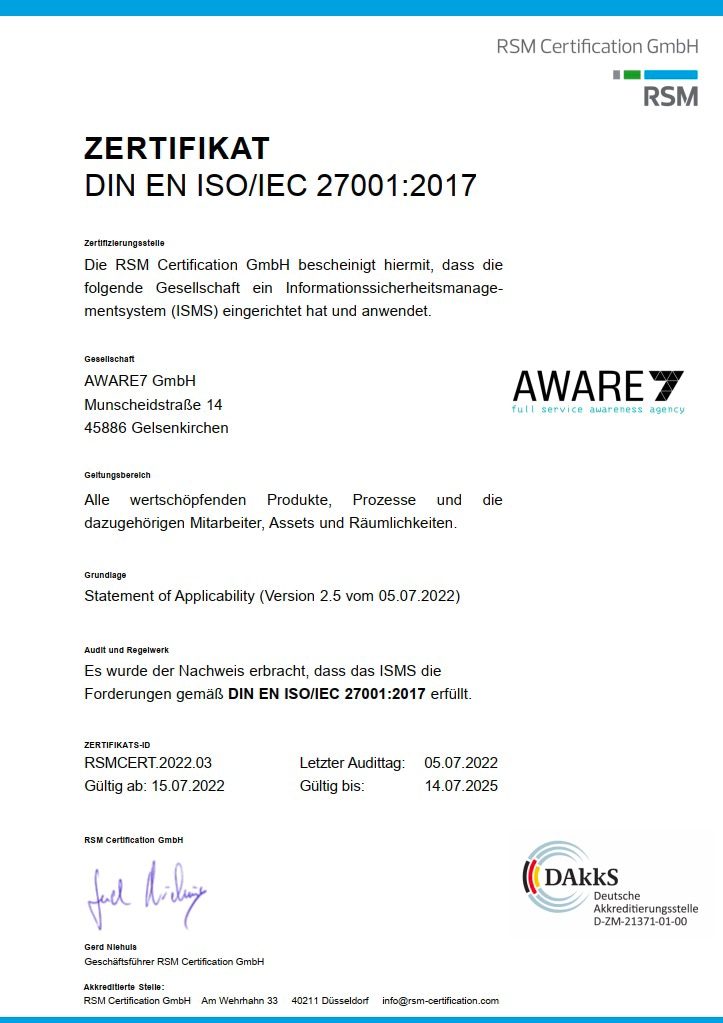
We are our best customer
As an information security consultancy, the demands placed on its own systems are high. All employees are aware that improvement as part of the PDCA cycle is necessary for an increased level of information security maturity.
We have decided to have our ISMS certified in accordance with ISO 27001 in order to be able to present this claim to the outside world. The scope includes all locations, employees, business processes and assets. The certificate can be downloaded free of charge.
We know what we are talking about, are familiar with the challenges of project planning and maintain close contact with auditors.

FAQ – Frequently asked questions
During a live hacking session, (certified) specialists demonstrate how a digital attack can be carried out. The target of the attack can be a company or a private individual.
From the theft of a password to a multi-layered attack and infection with an encryption Trojan, many interlinked aspects can be introduced during the demonstration. Organizers and live hackers should ensure through an exchange that the content of the show fits the target group, is understood and does not underchallenge them.
Most customers are interested in a show lasting between 30 and 90 minutes. Depending on the desired event format, the show can be extended to include a Q&A session.
Live hackers must also comply with applicable laws. This particularly affects §202c StGB. For training purposes, however, realistic live hacking can be carried out with a permit agreement, without the organizer or the lecturer being threatened with legal consequences.
Yes, live hacking addresses numerous aspects of digitalization. The aim is to empower the audience rather than deter them. The shows therefore also partly consist of tips and tricks for using digital media.
AWARE7 Live Hacking is available in English as well as German. Polish, Spanish, Turkish and Portuguese are available on request.
Yes, the show about security gaps and vulnerabilities can be carried out both remotely and on-site. Both formats have their advantages and disadvantages. Book a free appointment now to find out the best format for your event.
Yes, the show can be recorded under certain conditions. Multiple utilization is possible. The video can be used to fill your own e-learning module. After consultation, the video can also be made available on popular video portals. We will be happy to provide you with an individual offer, which you can find further details in.
If required, we can customize the live hacking to your organization. We recommend the recording, development and provision of live hacking as e-learning for individualization.

