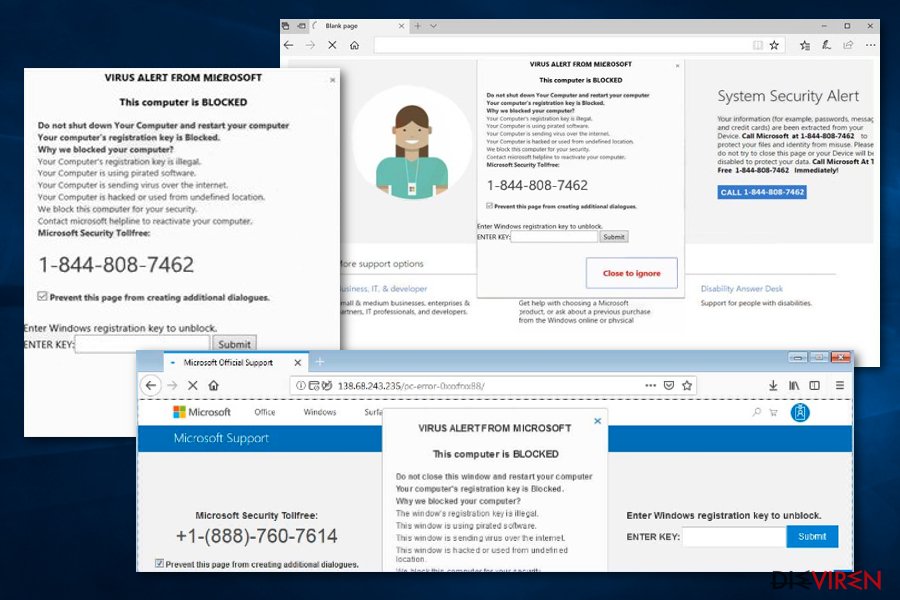
Through advertising or manipulated websites, people are tricked into accepting or making a call from Microsoft. With the help of fake warnings, pressure is exerted. The criminals want to gain access to the computer to encrypt data there and then blackmail the victims.
The call from Microsoft – a very popular scam!
A Microsoft employee calls and warns that your own computer is distributing viruses, Trojans and worms? Nothing can be saved on its own – the alleged Microsoft employee must immediately connect to the computer remotely to prevent further damage and to cushion potential costs.
This or similar is how the scam begins. The victims are addressed in different ways. Usually an advertising banner opens, but it is designed like a warning message.
It is often very difficult to click the advertisement away. An advertising blocker can prevent the advertisement from being displayed at that point. But criminals also contact their targeted victims by e-mail.
Especially inexperienced users* panic and call the phone number. The call center employees at the end of the line, who by no means work for or on behalf of Microsoft, are trained to put pressure on them.
It is assumed that their own computer is constantly infecting hundreds of computers. Often a medium three-figure sum is demanded, often around 400 EUR. Only then can the alleged Microsoft engineers solve the problem.
Tech Support Scam – Microsoft itself warns about it!
The success of the fraud scam is taking on such proportions that the concern is now issuing a warning itself:
- Official support requests are made by e-mail
- A call from alleged Microsoft employees should be terminated directly
Whoever takes these points into account does not fall for the swindlers.
Why is the call from Microsoft so critical?
The problem with the scam is that the scammers connect to the victims’ computers. The first action of the criminals is often to set a password, which is requested after rebooting.
Since the fraudster is then no longer on the computer, the scam continues. Often the potential victims do not notice anything. When the computer is restarted, the shock occurs.
This is how you can protect yourself from the Microsoft scam:
- Disconnect your computer from the Internet as soon as possible, have it checked by a specialist and change all passwords
The incidents can be reported on a form provided by Microsoft. In this way, the software company ensures that the mesh is contained. If you would like to know how such a scam works and how professionally the attackers proceed, take a look at the course of the scam:
You are currently viewing a placeholder content from Default. To access the actual content, click the button below. Please note that doing so will share data with third-party providers.

